
Business Impacts from Remote Working
Observations from a Social Engineering Security Assessment As a Threat and Vulnerability specialist, I regularly perform Social Engineering Assessments. These can consist of sending phishing
Your trusted source for unbiased cybersecurity insight.

Observations from a Social Engineering Security Assessment As a Threat and Vulnerability specialist, I regularly perform Social Engineering Assessments. These can consist of sending phishing

Having a clear and meaningful understanding of cyber security risk — such as one provided by a threat-informed and modeled security risk assessment — has

Security Risk Assessments Require Context To accurately understand security posture, context is needed. An organization must consider not only their controls, but also the most

Leveraging Threat Intelligence Simply put, we benefit when we think like a cyber-criminal and plan defenses around their tactics and attack methods. By leveraging threat

The Changing Threat Landscape Just as cyber defenses evolve, so do cyber criminals. They have made cyberattacks the fastest growing crime in the United States, and


There are parts of every business considered to be critical to its ability to function. Email, accounting, and customer service are a few. Indeed, if


This article was originally published in the Open Forum of the ISSA Journal for September 2019. The Open Forum is a vehicle for individuals to provide opinions
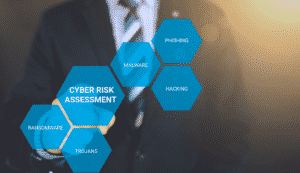

While meeting industry compliance is a must for financial institutions, the process by which compliance is met doesn’t paint a complete picture of an organizations’

This article was originally published by Security Magazine on June 25, 2019. Risk quantification has long been an imperative topic for security leadership, but now more than


This article was originally published by The Financial Revolutionist on June 3, 2019. You see it on the news almost every single day. Another security breach has
Subscribe today to our free eNewsletter for security insights, exclusive invitations, and more.
Your ace in the cybersecurity foxhole. Follow us on all your social media platforms.
Subscribe today to our free eNewsletter for security insights, exclusive invitations, and more.
© 2020 Alagen, LLC. All rights reserved.